Testing for Wordpress Exploits. Is there a way to do it?
I got a letter from my host telling me that there were some brute force password attacks coming from my server. I don't engage in any of that kind of wrongdoing, so I assumed that my server must have been compromized. I took everything down and reprovisioned the VPS. And I started everything up from scratch. I made backups before I brought it all down.
Perhaps my WordPress install was compromized and that's how someone compromised my server, I thought. Now I have a clone of the Wordpress site running in Virtualbox and I want to see if there's any kind of way to scan the Wordpress install and find out if there's any signs that it's been compromised.
I'd guess there's a plugin or script that can scan a WordPress installation for exploits.
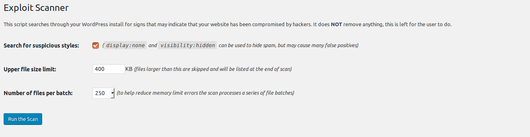
There's a plugin called Exploit Scanner. And it's made by Automatic, the people who make WordPress.
Okay, nevermind
The scanner gave a ton of results, much of them being pretty ambiguous. It seemed like there were a lot of false positives.
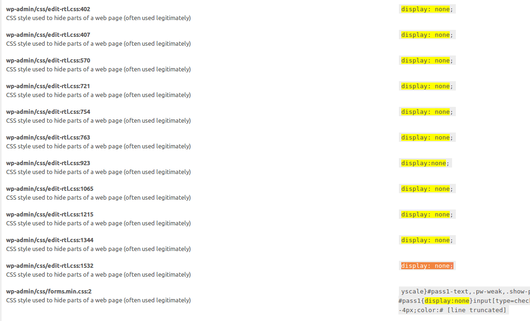
Here's an example. It reported a file:
wp-admin/css/edit-rtl.css:1532
CSS style used to hide parts of a web page (often used legitimately)
And then it just showed that this file had a CSS style that said:
display: none;
And that's not a terrible hack or anything. In fact, there were lots of lines like that. I guess I have to scan through them all to see if there's a rootkit or something serious.
Okay, forget that
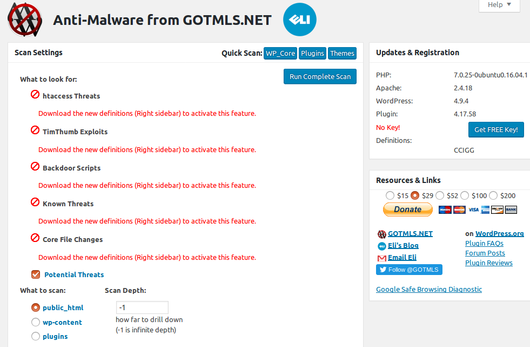
I uninstalled the Exploit Scanner and I found Anti-Malware Security and Brute-Force Firewall.
This plugin was described as:
This Anti-Malware scanner searches for Malware, Viruses, and other security threats and vulnerabilities on your server and it helps you fix them.
That sounded good so I installed it. There is a button that says "Run Complete Scan" so I clicked it.
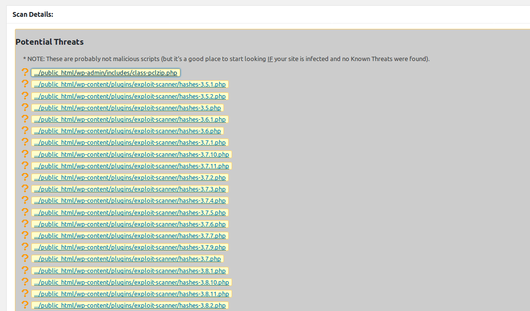
The results list was easy to understand and gave a list of potential threats. These were file names that I could click on and investigate. I didn't find any problems.
Everything Looks Good
I'm pretty pleased with the results of my WordPress malware scans. I don't think I have any exploits, going by these two highly rated WordPress exploit scanners. And I think I'm going to transfer my WordPress site, currently running in VirtualBox, to a live server.

